
Antivirus? Check. Firewall? Check. VPNs? Check. Proper VLAN segmentation? Check. Good backups disconnected from the network? Check. Multi-factor authentication? Check.
Sounds like you have it all when it comes to protecting your company from cyber-attacks, right? Well, if you don’t have regular security training for your end users, you’re still at huge risk. Phishing and social engineering efforts occur on a personal plane at many times – something your firewall or antivirus can’t necessarily stop.
Basically, you have to teach your employees how to avoid being tricked. They might be tricked into opening a malicious attachment or clicking a link in an email or they may receive a phone call from someone posing as IT support or the bank asking to wire money. Do you have the training and policies in place that would prevent these types of attacks from being successful?
Teach Your End Users to Be Suspicious
It’s important to conduct training on a regular basis updating your staff on the latest cybersecurity threats and to teach them methodologies to recognize bad actors. There will always be some new trend, the latest being an adorably-named “sextortion spam” in which a victim receives an email from a hacker claiming to have damning personal information.
However, the strategies to recognize suspicious emails or callers typically remain the same: assume unsolicited file attachments in email are dangerous as well as hyperlinks. Beware messages that contain impersonality like “Dear Sir” or “Dear Madam”. Question requests to do with finances, like wiring money or sending out W2s. It only takes a few seconds to contact the real people directly to verify.
It’s important to create a culture where this is top of mind and to minimize any fear of repercussions if a breach does occur. Staff may be more apt to try to cover up their mistakes rather than report them quickly. It’s also important to create a culture where no one is above doing these trainings and adhering to the policies, so get management and leadership to set the example.
Test Your End Users
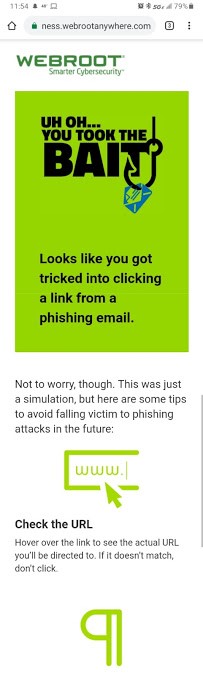
Some tools, like Webroot Antivirus, can be set up to send false phishing scams to keep your employees on their toes. This is a good method to help people start to recognize malicious requests. If you are serious about tightening your security or are subject to certain compliance regulations, you can sign up for penetration testing.
A consulting company will try to “hack” your organization in various ways and report back to you to show your vulnerabilities. This can be anything from testing the tools you have to your end user awareness to physical access.