
Veeam 12 Multi-Factor Authentication (MFA) – Veeam is now supporting OTP App MFA in their console application with the future release of Veeam Backup and Replication v12. There is preliminary work required, including some research, but it works.
Veeam 12 MFA – High Level
While you can only do so much with access to the server, you can block RDP to it (best practice) and force MFA on local accounts in Veeam.
Here is the snag: To turn on MFA you cannot use Groups, so you need to add your Administrator (or anyone else) individually, set Veeam permissions, and remove the default Administrators group.
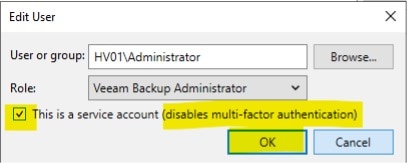
To skip/block any account from requiring MFA, you click on “this is a service account” and it won’t force MFA.
You then turn on MFA for the system, which enables MFA for the user that needs it and everyone else that is not a “service account”. It will prompt them with an app code, which you can cut and paste into an app such as Mobile Authenticator or ITGlue.
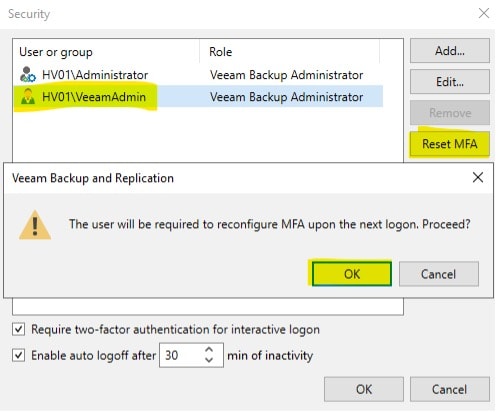
If access to that account is lost, you can reset MFA with another Veeam admin account. While this might not necessarily stop a malicious third party from trashing the on-premises server, it can help protect from remote access, your cloud repositories, and credentials with another layer.
Below is a deep dive of how to enable Veeam 12 MFA:
Veeam 12 MFA On A Standalone Server – Deep Dive
Step 1
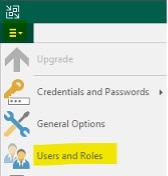
Make sure you have an recent backup of your Veeam Configuration before you start. Then Open the Veeam v12 Console and go to Users and Roles.
Step 2
You will notice the Veeam Backup Administrator is automatically assigned to Veeam Backup Administrators group. From here, if you have not already defined different roles to users, you can add them now as well:
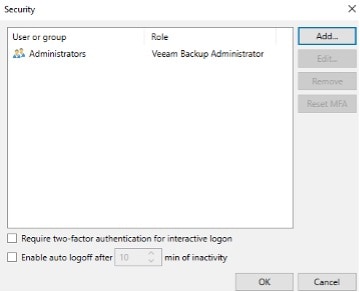
Here is list of the Groups:
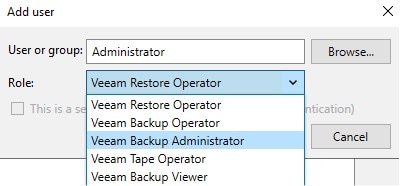
Here is a link to Veeam Support defining what those group roles are.
Step 3
Now we will add a user that is the Veeam Backup Administrator. Once the user is added, close Veeam:
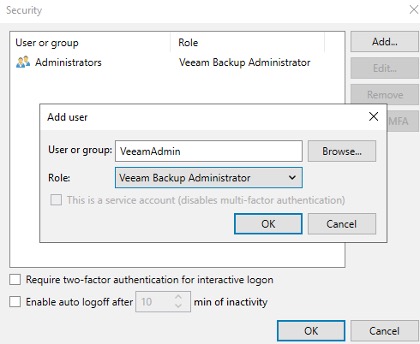
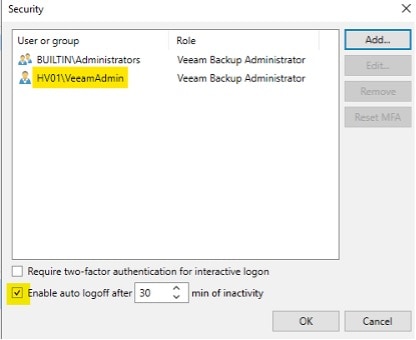
NOTE: You can also set it to log off users due to inactivity, which is another easy step to make sure a malicious user will not take over an account that was not logged out properly.
Step 4
When we reopen Veeam, we will change the Authentication method and use the local account and password we already have on the local server:
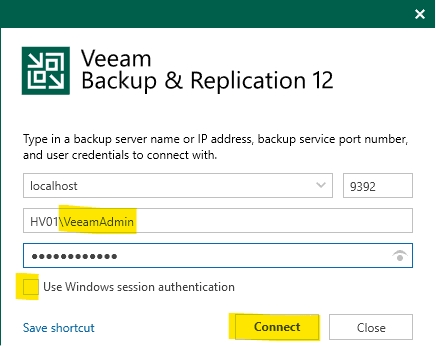
Notice we have not enabled MFA until we know we have access.
Step 5
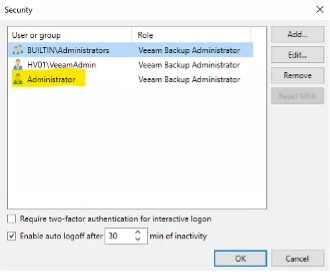
After you add the users, exit and log back on as the users individually to test before you enable MFA. Now I am adding a secondary account as a fall back if things go south with my initial MFA setup, and repeat the log off and on process.
Step 6
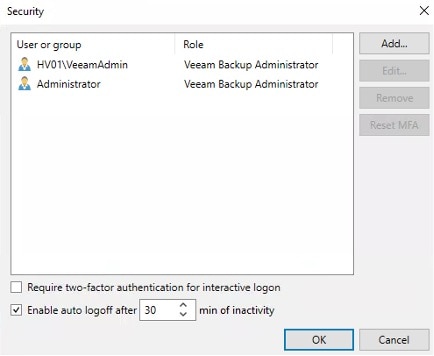
Now I will delete the BuiltInAdministrators group.
CAUTION: If you did not do the above steps and TEST your access, you could lock yourself out soon and be forced to reload. See Veeam configuration backup note above.
Step 7
Now I will enable “Require two-factor authentication for interactive logon” but DO NOT Click OK yet.
You need to Edit your users to setup your non-MFA account in case.
For this example, we will use Administrator and select “Edit”:
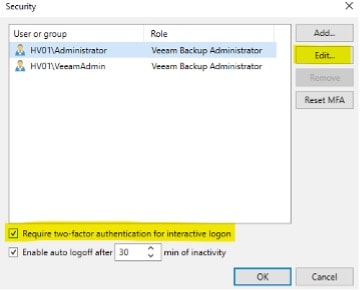
You will see “this is a service account” is no longer grayed out, so we will select that for this account so it does not require MFA:
For the VeeamAdmin account we will keep it as is:
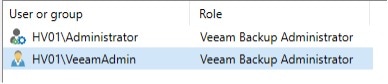
Note how the Administrator account icon has changed above.
Step 8
I will now log out and log back in as the VeeamAdmin and I should immediately be prompted to setup MFA using an authenticator app:


Congratulations! MFA is now set up on that account and you can repeat as needed for other accounts.
Whether you leave a “service account” without MFA enabled is your security call. But if you do, think through how you will strengthen it without Veeam MFA.
If someone’s MFA needs resetting, you can simply open up the Users and Groups with an active Administrator. Select the user and reset MFA as shown below:
At the end of the day as IT and Disaster Recovery administrators, security procedures should be included into everything we do. A well-designed, layered security strategy is the result of small details like requiring MFA for our crucial backups.
If you’d like to learn more about Veeam 12 MFA or if you have any additional questions, please contact us and call 502-240-0404 or email us at info@mirazon.com.
